LUSID has a Configuration Store to which you can upload secrets and parameters, in the same way as the AWS Parameter Store. You can then securely pull information from this central repository into applications in the LUSID ecosystem (such as Scheduler, Luminesce and the Notification service) on demand.
Note: You can also use the Configuration Store to override LUSID system settings.
You can store:
Secrets in obfuscated form. For example, you could store the credentials required by a Scheduler job, or by a Notification service webhook, or by a Luminesce provider. No-one else, not even a Configuration Store administrator, can reveal data you store as secrets. Read more.
Parameters in plain text. For example, you could store email addresses centrally and (coming soon) reference them in multiple different Notification service alerts.
You can upload information to:
Your Personal area of the Configuration Store. Only you can pull this information into LUSID ecosystem applications. Note a Configuration Store administrator may have sufficient access control permissions to administer your Personal area of the store, but they can never reveal your secrets.
The Shared area of the Configuration Store. Any LUSID user with appropriate entitlements can pull this information into LUSID ecosystem applications. A Configuration Store administrator may populate this area with suitable data for you.
Note: You can use the Block Reveal option to prevent a secret being revealed to any user, including you, once it has been saved.
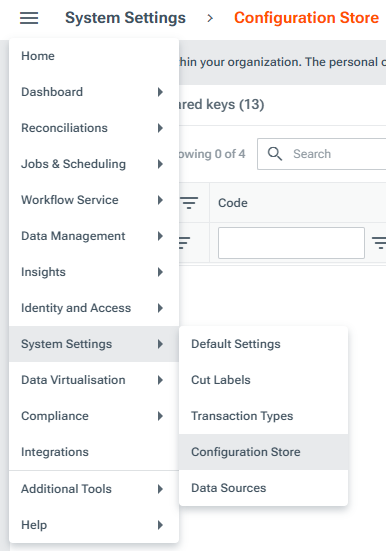
Providing you have appropriate access control permissions, you can upload to and administer the Configuration Store using the LUSID web app:
Alternatively, you can upload to and administer the Configuration Store programmatically:
Using the Configuration Store REST API
Using the Configuration SDK in various languages.
If you have a Luminesce license, using dedicated read and write providers.
Tutorials: Get started by doing something tangible
Reference: Understand concepts and implications
How-to guides: Get something done
